Lucy Wang believes that blockchain technology holds the key to the actualization of robust data security for the digital landscape. The Lambda co-founder made the call recently while talking about the recent Marriott Hotel data breach.
Data Breaches Aplenty
Breaches that end up compromising user data aren’t a new phenomenon on the internet. Almost every website with a significant volume of user information has fallen victim to hackers and other cybercrime syndicates.
Recently, Marriott International Hotel Group became the latest prominent name to admit being victims numerous data breaches. A statement released by the company said that as many as 500 million customers had been affected by multiple hacks beginning in 2014.
By the company’s admission, hackers successfully compromised user information such as credit card details, addresses, and even passport information. How could this happen? Well, all that data found its way unto centralized servers, providing a single point of failure that could be exploited by agents on the internet.
There are many within the decentralized technology landscape like Wang who believes that blockchain technology offers a solution to this problem. However, before going into such details, why should we even care?
Data is Valuable
Data is the currency of the digital economy, and as such, data is valuable. However, the present construct of the internet places user data in the hands of corporations that can pretty much do whatever they like with our precious information. They can sell them to the government (for surveillance) or to other companies (for targetted advertisements) both of which are horrible exploitation of user privacy.
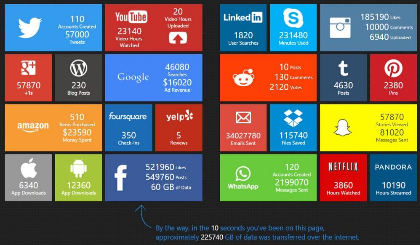
In the process of shopping, browsing websites, watching YouTube videos, reading various social information on the e-commerce platform, the algorithm will secretly monitor our behavior, and also collect our various data. In a sense, “data and the algorithm “knows” us more than ourselves. They know that we prefer juice or cola, we like beautiful models or men with eight packs of abdominal muscles. Like this Marriott case also shows that under certain circumstances, “data and algorithms” could have the “control right” of our wealth.
Data giants such as Google, Apple, Facebook, Tencent, Alibaba, and Baidu attract their attention by providing various information, services, and entertainment. And hotel giants like Huazhu and Marriott have our personal information and even bank card information. We have also seen that these “centralized” giants have used our data to earn hundreds of billions of dollars. We are not at all equal to the “centralized” giants.
Adopting Blockchain For Data Security

Under the centralized network, the giant almost has all of our private data, and the centralized internet has already relied heavily on the main-net. Whether it is academic or technical, these problems cannot be solved perfectly. In recent years, with the blockchain concept deeply rooted in people’s minds, the need to build a new decentralized network capable of subverting traditional client/server has gained more and more recognition.
However, most of the existing public chains are “ineffective” for data storage, TPS deficiency, cross-chain issues, governance issues, application development issues, etc. The nature of the blockchain is decentralized distributed ledger, and the data that can be stored is minimal (simple transaction records), other data cannot be efficiently stored. Therefore, in the absence of underlying data support, the actual use of the blockchain is significantly limited. More specifically, the decentralized storage of data is the most critical part of the future application of the blockchain.
To provide useful solutions to the problem, blockchain technology must of necessity, evolve with more robust and advanced features. Part of this improvement has to come at an algorithmic level like exists in projects like Lambda, with its Provable Data Possession (PDP) and Proofs of Retrievability (POR) protocols.


